Modern applications tend to have many distributed parts. For instance, you’d have message queues, storage buckets, serverless functions, servers, databases, and many more. So, it’s important to ensure that there is a standard way to access these components through a client.
Well, this is where Cloud Proxies come into the picture. For example, consider the following architectural diagram for an application that’s deployed on AWS:
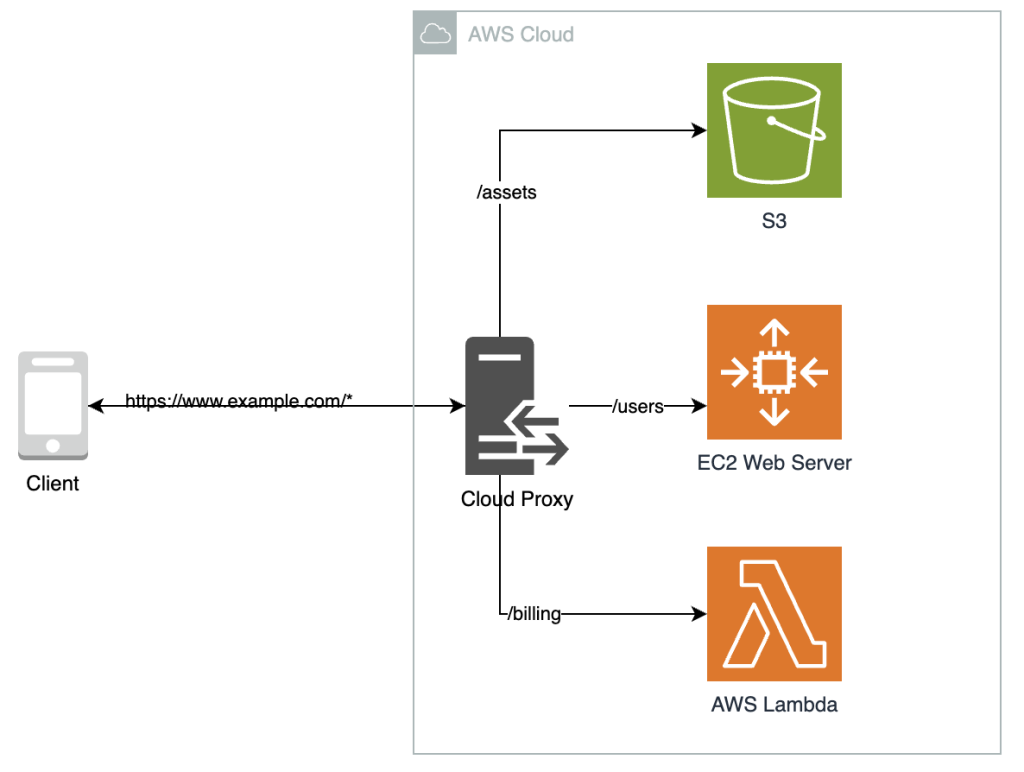
If you look at the diagram closely, you’ll see that the client only talks with one service – “Cloud Proxy”- which handles all the internal communication.
Simply put, a cloud proxy is a cloud-based system that connects a client to a web server, SaaS application, or data center. It acts as an intermediary between the client and server resources while providing a secure access point to a resource.
Why do you need a cloud proxy?
A typical cloud proxy proxy functions like this:
- A client requests flow through the cloud proxy to a resource (internet address/server).
- The reply from the resource returns through the proxy on their way to clients.
So, in a nutshell, it’s behaves like a “middleware” between your computer and the resource you’re trying to access. One good example of a cloud proxy is the Amazon API Gateway. For example, consider this architectural diagram:
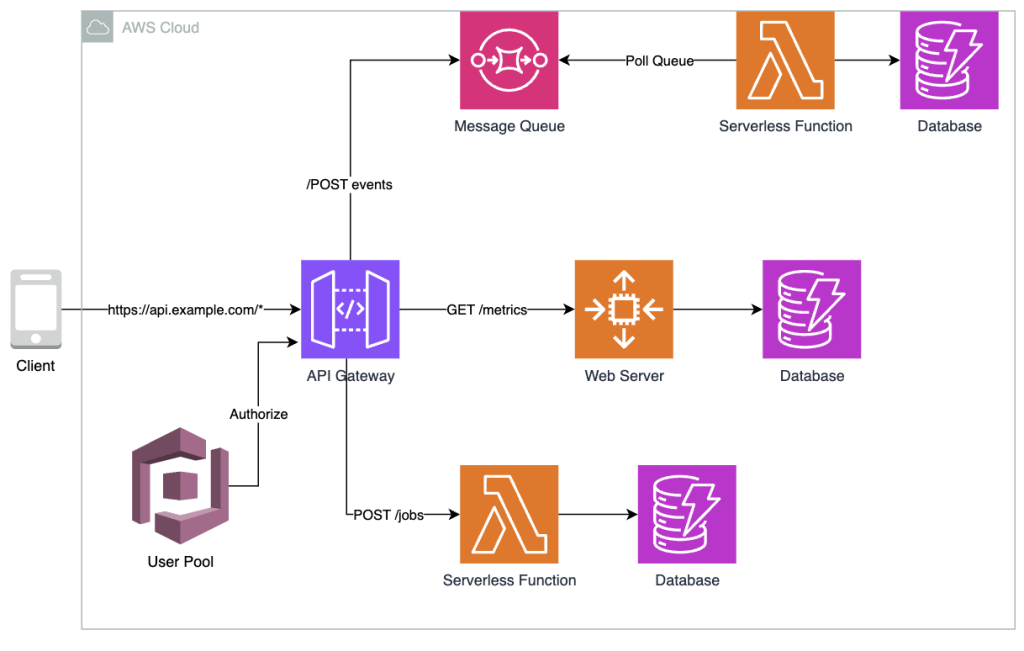
As you can see, there are many resources running in the cloud, from serverless functions and databases to message queues. By introducing the middleware – “the API Gateway”, it offers a central point of communication between the client and the resources that exist in the backend.
This ensures that the client and server never communicate directly but through the cloud proxy. The client’s requests are routed to the cloud proxy, then through a specified port in any applicable firewall, and finally to the content server before returning to the client.
Here’s a summary of how the cloud proxy works:
- The client sends a request, which the cloud proxy intercepts.
- Cloud proxy forwards the incoming request to a firewall if applicable.
- The firewall either blocks the request or forwards it to the server.
- The server sends a response through the firewall to the proxy.
- Cloud proxy sends the response to the client.
This process is identical to how a traditional proxy would operate. But, what makes it stand out is that it’s running in the cloud. So, it isn’t confined to data centre hardware like a conventional on-premise proxy. This all happens in near-real time regardless of traffic volume.
Additionally, by acting as a middleman, your cloud proxy can protect sensitive data (PII, PCI data) by adding layers of security. In this case, we’ve utilized a User Pool to authorize requests coming into the server to ensure only authorized users can communicate with the resource; however, you can utilize firewalls for protection as well.
What are the different types of cloud proxies?
There are three types of cloud proxies that you can leverage depending on your use case. They are:
- Forward
- Reverse
- Transparent
1. Forward Cloud Proxy
A forward proxy is an intermediary middleware between one or more user devices and the Internet. It acts on behalf of the client and routes the request to the destination. Next, it evaluates the response and forwards it back to the originating client.
By doing so, it offers benefits such as:By doing so, it offers benefits such as:
- Request Filtering: The forward proxy can enforce company policies related to Internet use by blocking access to certain sites or content based on predefined rules.
- Anonymity and Privacy: The forward proxy masks the client’s IP address with its own. This helps protect the user’s identity from external servers, thus enhancing privacy and security.
- Caching: A forward proxy can cache frequently accessed resources and immediately return the resource from the cache rather than sending the request out to the Internet. This reduces latency and improves the overall performance.
- Security: A forward proxy can provide additional layers of security, such as encrypting requests or scanning incoming content for malware and threats.
- Bypassing Restrictions: A forward proxy helps overcome issues with geo-restrictions, allowing users to access content that would otherwise be blocked in their region or network.
Reverse Cloud Proxy
A reverse proxy always sits in front of web servers to prevent clients and web servers from directly communicating with each other. Instead, all client requests are sent to the reverse proxy, which then forwards the request to the server. The response is then sent back to the client through the client proxy as well.
Using a reverse cloud proxy offers key benefits such as:
- Load Balancing: A reverse proxy can distribute client requests across several servers. This spreads the load evenly, preventing servers from becoming bottlenecks and thus enhancing a service’s scalability and overall performance.
- Security: Before the request is sent through to the web server, a reverse proxy can perform additional operations, such as validating the payload and authorizing the request to ensure that only legitimate requests are sent to the serve
Transparent Cloud Proxy
A transparent proxy (commonly known as an inline proxy) intercepts traffic flowing between the client and the Internet without requiring any configuration on the client. It gets its name as transparent as the user is unaware of the proxy; the proxy performs its operations silently.
By using a transparent cloud proxy, you can achieve:
- Content Filtering: Transparent proxies are used by organizations and ISPs (Internet Service Providers) to block access to inappropriate or harmful websites. They can enforce content policies by inspecting the content of web requests.
- Monitoring and Logging: They allow network administrators to monitor user behavior, log Internet usage, and compile reports on web traffic for analysis.
Tip: Evaluate your use case and consider using any one of the cloud proxies that’s covered here.
What are the benefits of cloud proxies?
Using cloud proxies can be extremely beneficial for an organization. Some of its key benefits include:
Scalability and Flexibility
Cloud proxies are deployed in the cloud. Therefore, it doesn’t have the restrictions of an on-premise proxy. Instead, it can leverage the benefits of the cloud, such as on-demand scalability.
Therefore, a cloud proxy can easily scale up and down based on the demand, seamlessly accommodating spikes in traffic without manual intervention, thus scaling the proxy well.
Additionally, the proxy can leverage the global cloud network and be available globally, ensuring that users can access their resources with a minimal round trip and thus reducing latency.
Cost-Effective
With a cloud proxy, you don’t need to invest upfront in physical infrastructure. Therefore, you save a lot of money that can be invested in other parts of your business.
Additionally, organizations can significantly cut down on operational costs as they no don’t need to maintain server rooms, power backups or cooling mechanisms as there’s no proxy infrastructure to manage.
Enhanced Security
Cloud proxy providers continually update their services with the latest security features to combat emerging threats, thus ensuring that your app can handle modern cyber attacks.
Additionally, cloud proxies can decrypt and inspect SSL/TLS encrypted traffic at scale. This ensures that validated requests are sent to the server, which on-premise proxies were not able to do due to limited resources.
Fun fact: Many cloud proxies are designed with a Zero Trust approach. This enhances security by verifying every request as if it originates from an open network.
Improved Caching
Cloud proxies can cache content closer to the user (in a point of presence (PoP) location), reducing load times and improving the user experience.
Additionally, it can use advanced routing techniques, such as geo-location, geo-proximity, or latency-based routing, to minimize round-trip times and improve overall performance.
Simplified Management
There’s two ways in which cloud proxies simplify management:
- Centralized Management: Cloud proxies can be managed from a central platform, simplifying administration and policy enforcement across the organization.
- No Physical Maintenance: There’s nothing physical about a cloud proxy. It’s all running in the cloud. So, organizations don’t have to manage anything on-site.
What are the use cases of cloud proxies?
Let’s take a look at some of the best use-cases for a cloud proxy.
Security
Cloud proxies act as middleware between the client and the server (resource), completely eliminating direct client-to-server interaction.
Therefore, the proxy can adopt security measures to ensure that only validated requests are accepted by the server. They can inspect and filter incoming and outgoing traffic, blocking potentially malicious content, malware, or phishing attempts.
Additionally, organizations can employ restriction rules to define who should gain access to a resource.
Load balancing
If your application leverages replicas of a server, you will have to distribute load evenly in your application for better scalability and performance. Therefore, you could leverage a reverse cloud proxy that sits in front of the web server, which seamlessly distributes the load between your cluster.
Web scraping
Cloud proxies go hand-in-hand when you’re building web scraping solutions. For example, if you were scraping a site daily, you’d likely be blocked from the site due to bot activity.
However, when you leverage forward cloud proxies, your IP addresses can be rotated or even replaced with the proxy’s IP address, making you unidentifiable to the server and allowing you to scrape content easily.
So, if this is something that you’re currently working on, build your scraper with Bright Data while leveraging its native cloud proxy to help mitigate issues with restrictions.
Concluding Thoughts
All in all, it’s important to understand cloud proxies and their use in building applications. Doing so could significantly improve your server resources’ performance, reliability, availability, scalability and security with minimal effort.